Resolv Postmortem: March 22, 2026 Incident
Apr 4, 2026
Opening Statement and Summary
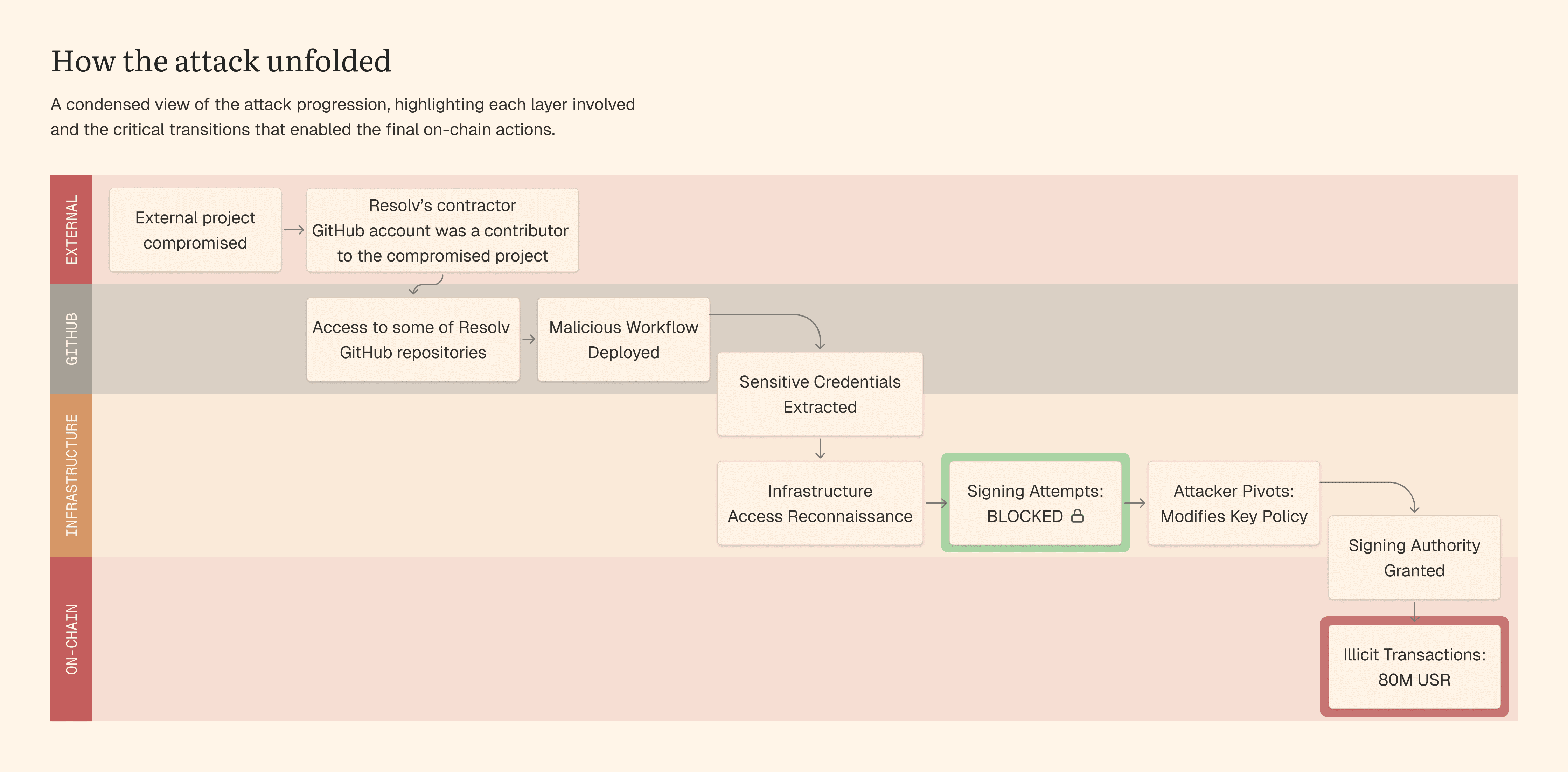
On March 22, 2026, Resolv's off-chain infrastructure was targeted through a multi-stage attack from outside the protocol's perimeter. The attackers gained unauthorized access to the signing infrastructure used by the protocol's on-chain services and executed two illicit transactions through the Counter smart contract, minting 80M USR and extracting approximately $25M in value as ETH.
Based on our investigation to date, we believe the exploit has been contained: the attack vector has been eliminated, all identified compromised credentials have been revoked, and most of the protocol's operations have been paused.
Approximately 46M USR of the illicitly minted supply has been neutralized through direct burns and the deployment of blacklist functionality. An active on-chain investigation is underway in coordination with counsel and blockchain forensics teams, and relevant authorities have been notified.
Pre-hack USR holders are being compensated on a 1:1 basis, with the majority of redemptions already processed. Resolv is further evaluating the broader impact and potential paths forward, with specific communications forthcoming.
An external forensic investigation is being conducted with the help of external security firms including Hypernative, Hexens, MixBytes, and SEAL 911. A further investigation and assessment is planned with a leading cybersecurity firm (Mandiant), blockchain Intelligence (ZeroShadow) and additional parties to strengthen confidence in the rebuilt infrastructure going forward. This document provides our account — based on currently available evidence, with an investigation still in progress — of what happened, how we responded, what we have learned, and what actions we are taking going forward.
How Resolv Works
Resolv is a DeFi protocol built around USR, a stablecoin pegged to the US dollar. Unlike fiat-backed stablecoins such as USDC or USDT, USR is backed by crypto-native collateral — including ETH, BTC, tokenized real-world assets, and select altcoins — with its dollar peg maintained through a delta-neutral strategy. Yield is generated from a combination of staking rewards and perpetual futures funding rates, and is passed through to USR holders via stUSR or wstUSR.
The protocol operates a two-tier risk architecture. USR represents the senior tranche: a lower-risk, stable-yield instrument. The Resolv Liquidity Pool (RLP) serves as the protocol's dedicated insurance and risk absorption layer. RLP holders accept higher risk in exchange for higher expected returns.
One of the permissionless ways to mint USR is through the Counter contract, which operates via a two-step process. A user first submits an on-chain minting request by depositing collateral. An authorized off-chain service then completes the operation by confirming the minting parameters and finalizing how much USR is issued. Both activities occur before any tokens are minted.
Collateral is managed through multiple custodians and top-tier security providers, with off-exchange settlement minimizing direct exchange counterparty exposure.
Attack Narrative — What Happened
The attack was not a single exploit but a multi-stage event, spanning multiple organizations and infrastructure layers.
Phase 1 — Initial Compromise (Outside Resolv's Perimeter)
Based on our current information, the attack chain originated from a third-party project where a Resolv contractor had previously contributed. When the third-party was compromised, the attackers obtained a credential with broad permissions. Because this credential was associated with the contractor's GitHub account, it provided the attackers with an initial foothold into Resolv's code repositories.
The circumstances of the initial upstream compromise are the subject of an ongoing investigation.
Phase 2 — Lateral Movement Within Infrastructure
The attackers used the compromised credential to gain access to some of Resolv's GitHub repositories and established a presence there. They then deployed a malicious workflow designed to exfiltrate sensitive credentials without triggering outbound network traffic detection.
After extracting the credentials, the attackers removed their own access from the repository to minimize their forensic footprint.
The extracted credentials provided access to Resolv's cloud infrastructure. Over the following days, the attackers conducted reconnaissance, enumerating services and attempting to extract API keys for third-party integrations.
Phase 3 — Execution and On-Chain Impact
The attackers' objective was to obtain signing authority over the cryptographic key used by the protocol's authorized off-chain service to complete minting operations.
The attackers' initial attempts to access the signing key were blocked by existing access control policies. Multiple distinct escalation attempts were denied before the attackers found a path that succeeded: rather than continuing to seek a role with pre-existing signing permissions, they used a higher-privileged role's policy management capabilities to modify the key's access policy directly, granting themselves signing authority.
The first illicit transaction was executed at 02:21:35 UTC (0xfe37f25...fc33743), minting 50M USR through the Counter contract.
Over the following approximately 80 minutes, the attackers began converting the minted USR into ETH through hundreds of DEX swaps, operating multiple wallets in parallel.
At 03:41 UTC, a second illicit transaction was executed (0x41b6b93...db1f18f), minting an additional 30M USR. Between and after both transactions, the attackers continued converting tokens to ETH at pace, extracting approximately $25M in total value.
Indications of illicit activity on cloud infrastructure led the team to revoke all identified compromised credentials, severing the attackers' access and terminating the active threat.
Detection, Response, and Containment
The protocol's real-time threat monitoring detected the first anomalous transaction and generated an alert. Within approximately one hour after the initial attack, the team had begun its response effort and began preparing to pause contracts, halt off-chain infrastructure, and revoke credentials.
Because the attack involved unauthorized access at the infrastructure level the response required identifying the attack vector and determining how the attacker had obtained signing authority before effective containment could be executed.
The team took a layered approach to containment. Backend services were halted first, reducing risk of minting and burning operations. At 05:16 UTC, all relevant smart contracts with available pause functionality were fully paused on-chain. At 05:30 UTC, the compromised credentials were revoked, severing the attackers' access to the cloud environment entirely. Forensic logs confirm that the attackers had been active as recently as 05:15 UTC, meaning the containment action terminated an active threat.
In the days following containment, the team executed additional recovery actions on-chain. Approximately 46M USR out of 80M illicitly minted were neutralized through direct burns and the deployment of blacklist functionality after the required timelock period.
External security firms were engaged to assist with infrastructure forensics, attacker profiling, and rapid audit of the contract upgrades required.
It is worth noting that several aspects of the existing security architecture performed as intended during the incident. Where the attackers accessed integration credentials, narrowly scoped permissions prevented unauthorized actions with the collateral pool assets. Production branch protections prevented malicious code deployment, forcing the attackers to pursue an entirely different path. The cloud infrastructure's access control model required the attackers to navigate multiple layers and attempt several distinct escalation paths, before they identified the method that ultimately succeeded. Real-time monitoring detected the first anomalous transaction promptly, enabling the team to begin incident response.
Root Cause Analysis
The exploit was not the result of a single vulnerability. It required the attackers to discover and chain together a series of individually limited security gaps — spanning multiple organizations and infrastructure layers. No single issue in this chain would have been sufficient to execute the attack on its own.
The following analysis is based on currently available evidence, with an independent investigation still in progress. We present the contributing factors in the order the attackers encountered and exploited them.
The attack originated outside Resolv's infrastructure. A credential associated with a contractor's GitHub account — retained from a prior engagement with a third-party project — provided the attackers with an initial foothold. The circumstances of the upstream compromise are the subject of an ongoing investigation.
The attackers used this foothold to access Resolv's GitHub repositories and extract infrastructure credentials. The attackers exploited an organization’s GitHub repositories settings to gain access, then deployed a malicious workflow that exfiltrated sensitive credentials. The production branch was protected by mandatory manual approval for merges, meaning the attackers could not have deployed malicious code to production through this vector.
Within Resolv's cloud infrastructure, the threat actors conducted reconnaissance before attempting execution. Using the extracted credentials, the attackers accessed cloud infrastructure and spent time enumerating services and attempting to extract API keys for various third-party integrations.
Obtaining signing authority required the attackers to navigate a complex infrastructure access model. The cloud infrastructure's key management service required both identity-level permissions and a separate key-level access policy to be aligned before signing operations could be performed. The attackers encountered repeated failures before identifying the method that ultimately succeeded — using a higher-privileged infrastructure role to modify the key's access policy itself.
Once the attackers obtained signing authority, no independent on-chain mechanism constrained the resulting minting operations. The protocol's minting mechanism relied on off-chain controls to ensure that the proper amount of tokens were minted once valid collateral had been deposited. This design meant that the infrastructure breach translated into significant on-chain impact. Remediation actions addressing this are described in Section 6.
Remediation — Actions Taken and Planned
Additional security enhancements are not disclosed in detail to avoid overexposing internal infrastructure — an approach consistent with industry practice for post-incident disclosures.
Immediate containment (within hours of the incident):
All compromised credentials were revoked and rotated across all infrastructure services, including CI/CD credentials, cloud infrastructure API keys, exchange and custodian integrations, public keys held through third-party security providers, authentication services, and VPN access. All relevant-to-the-attack smart contracts with available pause functionality were paused. Personal access tokens were prohibited across the GitHub organization.
On-chain recovery actions:
Approximately 46M USR out of ~80M illicitly minted was neutralized through direct burns and the deployment of blacklist functionality after the required timelock period.
In progress and planned (targeting completion before protocol restart or before usage of the related component in production):
Replacing CI/CD credentials with OIDC or equivalent based authentication and restructuring infrastructure permissions to ensure signing operations cannot be reached through CI/CD credential chains
Implementing on-chain mint caps and oracle-based price validation for minting operations
Deploying automated emergency pause mechanisms connected to real-time monitoring
Enhancing anomaly detection and alerting for infrastructure access patterns
Implementing restrictive GitHub organization permissions and conducting a comprehensive external security review
A comprehensive investigation into the incident is being conducted with outside counsel and external security firms.
Impact on Users and Path Forward
Pre-hack USR holders are being compensated on a 1:1 basis. The majority of redemptions for pre-hack USR holders have already been processed or are in the pipeline.
The Company is evaluating the impact on others and potential paths forward. Specific terms and outcomes will be communicated separately to affected parties through dedicated channels.
Most of the protocol's operations are paused until further notice. Priority is being given to safe management of the collateral pool, processing of eligible redemptions, and completion of the security investigation and infrastructure remediation. We will provide further updates on the timeline for further protocol operations.
On-Chain Investigation and Fund Recovery
Approximately 46M USR out of 80M illicitly minted has been neutralized. The investigation into the remaining illicitly minted USR is ongoing.
An active on-chain investigation is underway, conducted in coordination with outside counsel, blockchain forensics teams, and on-chain analytics firms. Relevant authorities have also been notified. The investigation encompasses both the tracing of stolen funds and the identification of the threat actors responsible.
Major exchanges and asset issuers have been notified and are cooperating with the investigation. Detailed on-chain tracing results and attacker attribution are not being disclosed at this time to avoid compromising ongoing recovery efforts. Any recovered funds will be factored into the resolution plan.
Broader Industry Lessons
This incident highlighted vulnerabilities that are not unique to Resolv. We share these observations to contribute to the ecosystem's collective security posture.
Supply chain risk from cross-organizational credentials. The attack originated from a compromised third-party project. As developers contribute to multiple projects and organizations, unrevoked or overly broad credentials may create bridges between otherwise isolated security perimeters. This class of supply chain risk is a growing concern across the industry.
CI/CD workflows as an attack surface. The attackers exploited CI/CD workflows to exfiltrate infrastructure credentials without triggering outbound network traffic detection. This is a growing class of attack that the industry is increasingly recognizing as a first-order security concern.
On-chain safeguards as a defense-in-depth layer. The frequent reliance on off-chain operational controls as the main constraint on privileged on-chain operations represents a systemic risk. Smart contracts governing high-value operations benefit from independent limits — per-transaction caps, per-period caps, oracle-based validation — regardless of how well the off-chain infrastructure is secured.
Automated response capabilities for time-sensitive operations. Emergency pausing of smart contracts should not depend on human coordination under duress. Monitoring systems that detect anomalous on-chain activity should be capable of triggering automated pause actions.
Acknowledgments
We would like to acknowledge the external teams and individuals who contributed to the incident response, forensic investigation, and recovery efforts:
Hexens — infrastructure forensic analysis and attacker profiling
MixBytes — rapid security audit of smart contract upgrades deployed during the recovery process
SEAL 911 — emergency coordination and response support
Hypernative — real-time threat detection, monitoring, and proactive team outreach and cooperation
We also thank the DeFi protocols and integration partners who coordinated swiftly during the response, and the community security researchers who contributed independent analysis.
